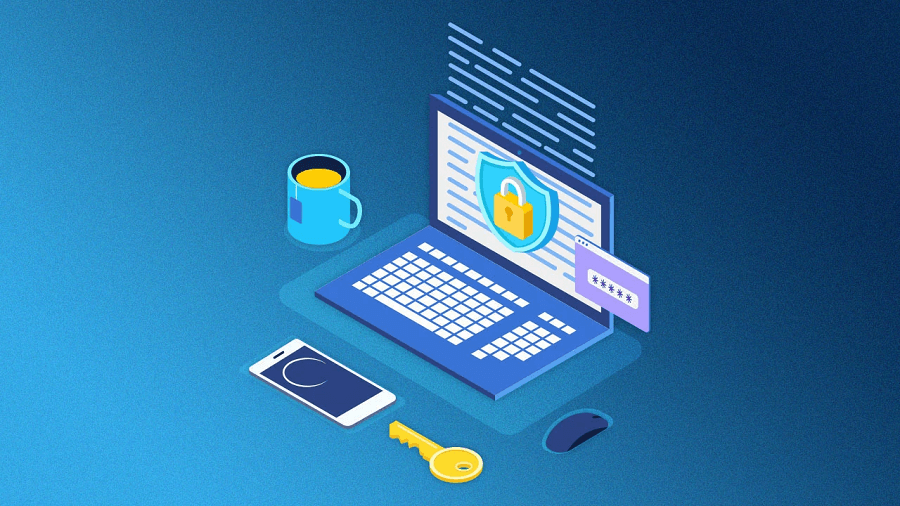
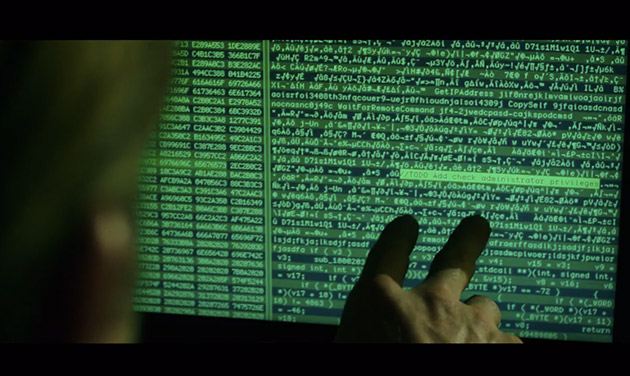
Massive Data stolen and left on a naked server by Lebanese hackers

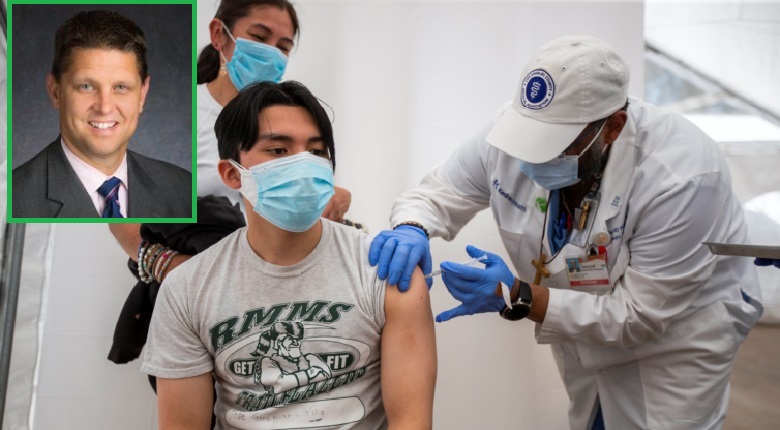
A report released today, from the Electronic Frontier Foundation and Lookout (mobile security company) about a mass hacking campaign dubbed Dark Caracal. It was believed that the alleged hacking campaign was managed by the GDGS (General Directorate of General Security) of Lebanon. It is one of the intelligence agencies in the country. The information was collected from a large number of victims from more than 20 countries using surveillance efforts since 2012. Their major goals added military personnel, activists, journalists, manufacturing companies, and financial institutions. There was also some stolen data, including cell records, documents, contact information, texts, and photos. A researcher of Lookout security, Michael Flossman said in a press statement that it was everything.
The intruders used harmful apps and they duplicated authorized communication platforms, such as WhatsApp and Signal to steal the cache of data. They loaded up fake versions with harmful viruses and it enabled them to record the conversations of users. The Staff Technologist of EFF, Cooper Quintin issued a statement that one of the most amazing approaches regarding this alleged attack was that it didn’t need an advanced or expensive activity. The entire Dark Caracal requirement was regarding application permissions that users allowed them during the download process of the alleged apps without knowing that there desired app contains malware. The intelligence head of Lookout, Mike Murray said that the storage of stolen data wasn’t skeptical and they left entire data naked online on an unprotected server.